Sender-controlled private email Electronic privacy with EPRIVO
Digital privacy, including the vulnerability of emails to privacy violations, is a growing concern for consumers and organisations alike. Private emails are susceptible to threats from both socio-economic and technological aspects. Unauthorised access can occur during the transit of an email to its recipient as well as during storage on a device, at a recipient, email server or in the cloud. The research and development team at cyber-security firm BlueRISC Inc. are addressing broad privacy solutions including enabling private collaborations. A current effort relates to email privacy issues and the broader question of private collaborations. The team is led by Dr Csaba Andras Moritz, Founder and Chairman of BlueRISC Inc. and Professor of Electrical and Computer Engineering at University of Massachusetts Amherst.
Email vulnerability
Users can accumulate numerous emails that are regularly archived for many years and spread across multiple vendors in the cloud. These emails are exposed to privacy violations throughout their lifetime. Together with factors relating to the sender and associated providers, as soon as an email is sent its privacy will also depend on the recipient’s security habits, their devices and their providers in the cloud. Throughout the development of EPRIVO, the researchers have taken these multi-faceted threats to privacy into account. They encompass both socio-economic and technical factors that lead to most people’s emails being compromised at some point.

Socio-economic threats
Socio-economic threats can be underpinned by societal factors such as money, politics, power, culture and religions. While these factors can be considered part of everyday life, they can also be described in the terms and conditions that form agreements between parties or in terms of privacy. Prime examples of this are the free services that require users to agree to their terms and then use the users’ information to target advertisements as part of a monetization scheme.
Within one’s Electronic Privacy Circle,
one should be able to maintain privacy and control access to information anytime in the future.
Considering this socio-economical context, email privacy can be vulnerable to data mining by both service providers and storing companies for financial benefit. There is also the possibility of future changes in their terms and conditions that can potentially compromise the consumer’s information. Furthermore, such email privacy violations can happen without the user’s knowledge.
Technological threats
The technology employed by users, their service providers and their storing companies to maintain information security can provide gateways for email privacy to be exploited. In addition to the risks arising from weak user passwords, all three parties are susceptible to attacks from hackers, phishing and social engineering together with implementation vulnerabilities. There is also the possibility of security breaches involving service provider insiders.
The research team at BlueRISC Inc. have solved a number of critical issues in order to address email privacy. They also recognise that a conflict of interest associated with privacy promised by organisations that directly benefit from users’ information exists, and they note that even with government regulation, this privacy is unlikely to materialise.
Role separation
The researchers stress that in order to manage privacy, the roles of those who store our information and those who provide security, or privacy for it, have to be separated from one another in order to remove the existing conflict of interest.
Future privacy
It only takes a single compromise at any time for our email privacy to be violated. Given the constantly changing threat models, together with the regular discoveries of new digital security vulnerabilities, the future privacy of secure emails in cloud models will still have to be guaranteed for users.
True owner of a communication?
Furthermore, senders require privacy controls in order to protect their email privacy long-term, both on recipients’ devices and in the cloud.

Moreover, the team is facing the challenge of solving the trade-off between legal access and yet still maintaining privacy without opening backdoors (ways of bypassing normal authentication or encryption) into systems.
Electronic PRIvacy Circle (EPRIVO)
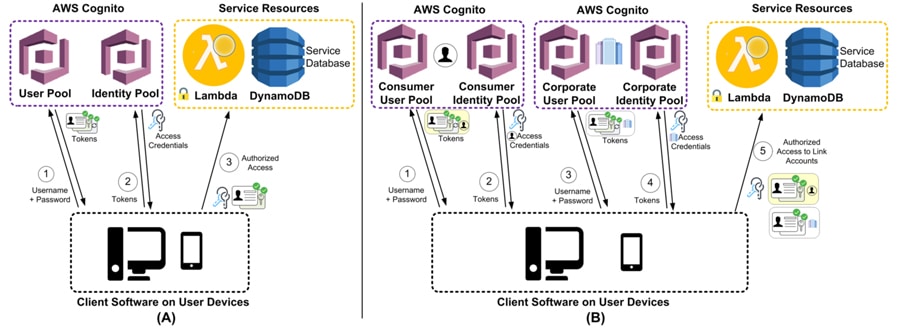
BlueRISC Inc.’s team is addressing these challenges with the development of the concept of Electronic Privacy Circle, which is where the EPRIVO name is derived from. They are creating and supporting privacy collaborations and access to information with cryptographically enforced privacy controls. EPRIVO is available to both individual consumers and organisations and it operates on both mobile and desktop platforms. With its initial focus on private messaging through emails, in the form of both voice and text, the researchers are aiming to enable a private data collaboration system that performs private information management and sharing together with associated communication. The researchers believe that “within one’s Privacy Circle, one should be able to maintain privacy and control access to information anytime in the future and independent if information is in the cloud or recipients’ devices.”
Moreover, the EPRIVO approach is unique in that offers its users’ security for their existing email accounts as well. There is no requirement to create a new email address as EPRIVO supports existing emails. The vision is that everything we use today as communication will be possible to turn into private.
Ownership dilemma: Sender-controlled email privacy
Through a combination of cloud-based authentication and cryptographically enforced access, the EPRIVO team introduced a new pioneering approach that allows senders to forever maintain control of sent content, including in the cloud and recipients’ devices. Senders are enabled to maintain full control of each private email for the entire lifetime of that message, even after the email has been sent. The sender can take back the email at any time, or erase it from both the recipients’ devices and the cloud if they want to. The sender can also prevent the recipient from forwarding the email and set an expiration time for the message. In addition, EPRIVO allows its users to privatise old emails by enabling the archiving and encrypting of any old email message from any email account. EPRIVO was initiated by Dr Moritz and is primarily funded by BlueRISC. DHS-funded research aspects deal with exploring roots of trust in a cloud-based environment, and especially in a corporate setting.
EPRIVO does not store emails. Instead, it employs algorithms to shuffle emails through the users’ own email carriers.
Securing emails against threats
EPRIVO offers a patented email-privacy approach that is not susceptible to the socio-technological issues mentioned above. It combines government-grade digital security together with physical security, in the form of physical separation that is implemented in the cloud. This physical security means that no carrier or provider will have access to the complete message, even encrypted emails. Furthermore, EPRIVO does not store emails or content. Instead, it employs algorithms to shuffle emails through the users’ own email carriers with the result that it never needs to store them. This means that EPRIVO can manage service and access throughout the world without having to maintain or fund the worldwide data centres. This is also a healthy separation of roles between content-storing providers and companies that provide security, avoiding any conflict of interest.

Whilst the security is managed by EPRIVO, the email messages are kept fully encrypted in the users’ email accounts. Users select the privacy features that will define how their messages are stored, retrieved, or destroyed. Users can also send a secure, confidential, encrypted email to non-EPRIVO users.
Societal threats are avoided as a provider cannot exploit an email’s content as it is encrypted. Access to the complete email is impossible, even if digital security is compromised due to EPRIVO’s physical separation. Similarly, technological threats are prevented as a security breach of a service provider or storing companies cannot endanger email privacy. To a certain degree EPRIVO can also provide security cover for the users’ carelessness in terms of their security habits. If a user’s email password is compromised, or if someone hacks into one of the carriers, the emails’ privacy remains untouched.
A solution pioneered and patented relates to how access to information on the internet can be allowed. An approach requiring a multi-party agreement, across multiple providers, that uses cryptography creates a new fair mechanism to potentially support legal access.
EPRIVO’s versatility
EPRIVO can be integrated with all platforms and devices. It supports email-client software and web-based email access. It can be used for existing email addresses from any provider. It can be used for private text, attachment, as well as, voice responses or voice emails. Undoubtedly it moves usability to the fore and removes the burden of managing security management from its consumers.
Professor Moritz encapsulates EPRIVO as “the first Private Email Service enabling users to add innovative privacy controls, authentication, and encryption while using their existing email addresses. Sent private emails can be recalled anytime to make them vanish everywhere. A new form of collaboration that has privacy at its forefront is made possible.”
Personal Response
How did you develop the privacy architecture supporting EPRIVO?